Security
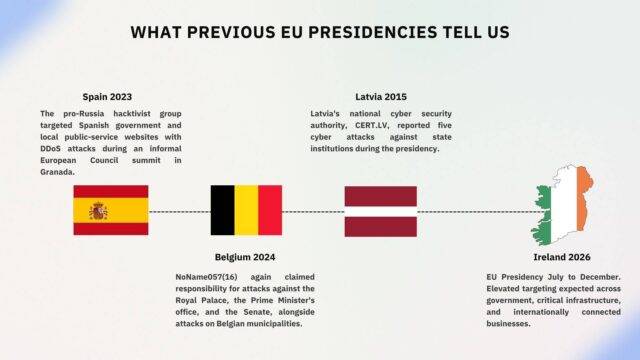
Ireland EU Presidency 2026: Cyber Security Risks and What Organisations Should Do

Threat Intelligence Bulletin: FIFA 2026 World Cup

Ekco Secures Nerdio Gold and Mimecast Elite MSP Status to Expand Security-led Cloud Services
Iran Cyber Attacks 2026: Threats, APT Tactics & How Organisations Should Respond

Insider threats: Seven steps to protect your organisation

How to Lead a Cyber Incident Effectively

Chasing the Kitten: A Closer Look at Targeted Threat Hunting with Ekco

5 Smarter Ways to Build Your Cybersecurity Budget

Lessons learned from a chilling encounter with a spider
Ekco Launches All-in-One, Enterprise-Grade Cybersecurity Offering to Protect SMBs

Rapid Remediation: How Ekco Tackled the Latest Veeam Vulnerability

Keeping Ahead of Hackers – Insights from our Legal Sector Roundtable

Question?
Our specialists have the answer
