Blog
Iran Cyber Attacks 2026: Threats, APT Tactics & How Organisations Should Respond

Insider threats: Seven steps to protect your organisation

Ekco acquires Datalogix

How to Lead a Cyber Incident Effectively

Chasing the Kitten: A Closer Look at Targeted Threat Hunting with Ekco
Ekco invests €10M in Caribbean expansion and new office

Six Nations 2026 Threat Intelligence Bulletin
Cybersecurity in 2026: Three Predictions from Ekco Experts
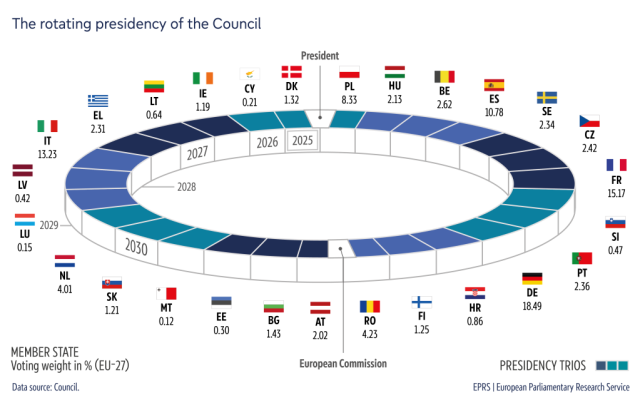
Cybersecurity Risks of the EU Council Presidency

Checklist: Is your organisation ready for Copilot?
Cloud confidence in 2026 starts with what you do now
5 Microsoft Ignite announcements you should care about

Question?
Our specialists have the answer
