Blog
Cybersecurity in 2026: Three Predictions from Ekco Experts
Cloud confidence in 2026 starts with what you do now
5 Microsoft Ignite announcements you should care about
Microsoft Ignite 2025
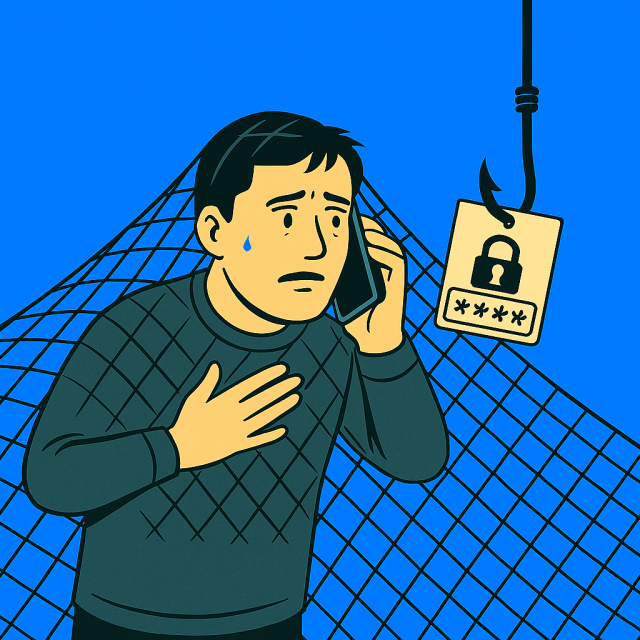
Caught in a vishing net

Karen Morton Shortlisted for Tech Leader at the 2025 Diversity in Tech Awards

Microsoft Announces Changes to MFA and Authentication Management

Important changes to default outbound access in Azure coming this September

The Ekco Chamber: Q2 – July Edition

Copilot in Practice: Strategic, Secure, and Supported

Ekco expands in Ireland as Adapt IT joins the team

54% of organisations flying blind on cloud costs as hybrid adoption surges

Question?
Our specialists have the answer
