Business Email Compromise
Suffered or suspect an email breach?
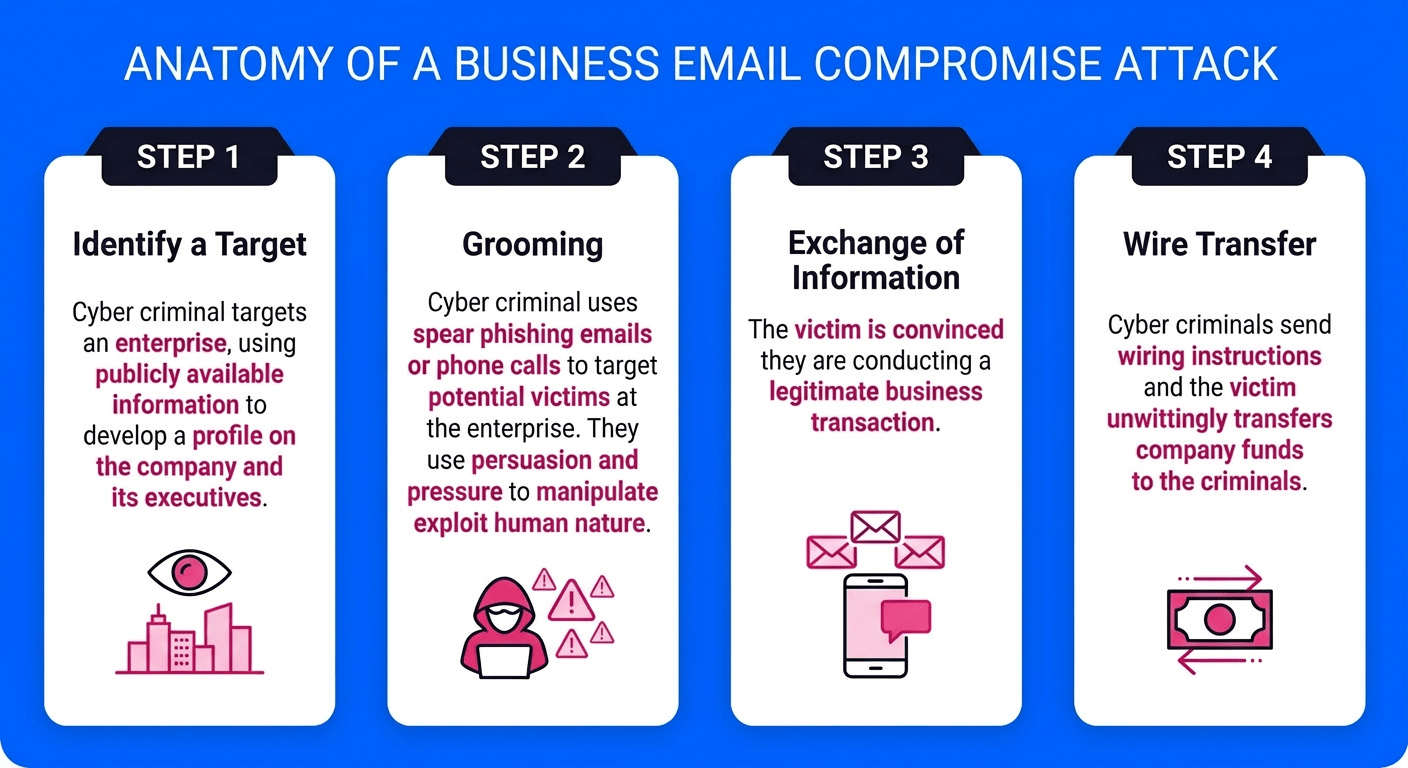
How this happens
Currently the main source of email compromise is through a verified and trusted 3rd party or supplier. That organisation suffers a breach and unbeknownst to them the threat actors are using their legitimate email system to inject themselves into conversations around invoices and redirecting payments elsewhere.
BEC represents the most financially devastating form of cybercrime after extortion (ransomware). Early detection and a swift, expert response are absolutely critical to minimising damage and recovering funds.
Find out about your obligations & liability here through our neighbouring firm at Dillon Eustace Insights
Business Email Compromise
Impersonation Scams
Cybercriminals impersonate trusted individuals or entities to trick employees into authorising fraudulent payments or disclosing sensitive information.
Highly Targeted
Unlike mass phishing campaigns, BEC attacks exploit deep research and social engineering to bypass technical defences by manipulating human trust.
Financial Fraud
CEO fraud, account compromise, and vendor impersonation schemes result in fraudulent wire transfers, invoice redirects, and payroll fraud.
How our Incident Response Team can help
1. Identification & Containment
- Validate indicators and confirm what is actually happening
- Establish whether containment has truly been achieved
- Preserve evidence & define timeframe of compromise
- Proactively hunt for additional malicious activity
Ensuring the Threat Actors have been kicked out and no other users will fall foul
2. Investigation & Analysis
- Reconstruct attacker paths
- Validate hypotheses with evidence
- Define blast radius and impact
We state what is known, what is unknown and what is being tested. No step forward without evidence.
3. Reporting
- Full incident narrative
- Root cause and attacker techniques
- Regulatory-ready documentation
- Actionable security improvements
Strong reporting protects executive accountability and supports NIS2 obligations.


